17 Travel Scams Targeting Tourists in 2026 — And How to Avoid Them
As global tourism rebounds to unprecedented levels in 2026, reaching an estimated 1.8 billion international arrivals, travelers face an increasingly sophisticated array of scams designed to exploit their unfamiliarity with local customs, languages, and technologies. The digital revolution has not only transformed how we travel but has also revolutionized the methods scammers use to target unsuspecting tourists. From AI-powered deepfake videos used in romance scams to blockchain-based cryptocurrency theft schemes, modern travel fraud has evolved far beyond the simple pickpocketing and overcharging tactics of previous decades. Today's scammers leverage advanced technology, psychological manipulation, and detailed social media reconnaissance to create elaborate schemes that can drain bank accounts, steal identities, and ruin dream vacations. The financial impact is staggering, with travel-related fraud costing tourists an estimated $24 billion globally in 2025, a figure projected to rise by 15% in 2026. Understanding these evolving threats is crucial for modern travelers who must navigate an increasingly complex landscape where traditional street smarts must be combined with digital literacy and cultural awareness to ensure safe and enjoyable journeys.
1. The Fake QR Code Menu Scam

The digitization of restaurant services has created a perfect storm for scammers who exploit tourists' reliance on QR code menus, particularly in popular tourist destinations across Asia, Europe, and Latin America. This sophisticated scam begins when travelers scan what appears to be a legitimate QR code at a restaurant table, only to be redirected to a fraudulent website that mimics the establishment's actual menu. The fake site often features inflated prices, hidden service charges, or most dangerously, payment portals that harvest credit card information and personal data. In some variations, the QR code installs malware on the victim's device, providing scammers with ongoing access to banking apps, email accounts, and stored passwords. The scam is particularly effective because tourists are already in an unfamiliar environment and may not immediately recognize subtle differences in website design or pricing structures. Restaurant staff may be complicit, directing customers to specific tables with compromised QR codes, or the scammers may simply place stickers with malicious codes over legitimate ones. To protect yourself, always verify QR codes by asking restaurant staff directly, manually typing restaurant websites into your browser, or using established food delivery apps instead of scanning unknown codes. Additionally, never enter payment information through a QR code-generated website without first verifying the URL matches the restaurant's official domain.
2. AI-Generated Romance Scams on Travel Apps

The integration of artificial intelligence into dating and travel companion apps has given rise to an entirely new category of romance scams that specifically target lonely travelers seeking connection abroad. These sophisticated operations use AI-generated profile photos, chatbots capable of maintaining convincing conversations in multiple languages, and detailed knowledge of local attractions to create seemingly perfect travel companions. The scammers typically approach victims on popular travel apps, social media platforms, or dating services, presenting themselves as attractive locals or fellow travelers with extensive knowledge of the destination. The AI systems can maintain multiple conversations simultaneously, adapting their personalities and interests to match each victim's preferences while gradually building emotional connections over days or weeks. Once trust is established, the scammers introduce various financial requests: emergency medical expenses, visa problems, family crises, or investment opportunities in local businesses. The most insidious aspect of these scams is their ability to provide real-time responses and maintain consistent backstories across multiple interactions, making them nearly indistinguishable from genuine connections. Victims often realize they've been scammed only after sending substantial amounts of money or sharing sensitive personal information. To avoid falling victim, never send money to someone you've only met online, conduct reverse image searches on profile photos, insist on video calls at random times, and be wary of individuals who seem too perfect or eager to meet your specific travel interests.
3. Cryptocurrency ATM Tourist Traps

The proliferation of cryptocurrency ATMs in major tourist hubs has created new opportunities for scammers to exploit travelers' curiosity about digital currencies and their unfamiliarity with local financial systems. These scams typically occur near popular tourist attractions, airports, and shopping districts where legitimate-looking cryptocurrency ATMs are strategically placed to attract curious travelers. The machines often advertise attractive exchange rates or promise easy conversion between traditional currency and popular cryptocurrencies like Bitcoin or Ethereum. However, these fraudulent ATMs are designed to steal both traditional currency and personal information while providing worthless tokens or no cryptocurrency at all. The scam works by encouraging tourists to insert cash or credit cards while providing extensive personal information including passport numbers, home addresses, and phone numbers under the guise of regulatory compliance. Some sophisticated versions even provide fake transaction receipts and temporary wallet addresses that appear legitimate but actually direct funds to scammer-controlled accounts. The victims often don't realize they've been scammed until they attempt to access their cryptocurrency later, finding empty wallets or discovering that the provided wallet addresses don't exist. To protect yourself, only use cryptocurrency ATMs from established, verifiable companies, research the machine's operator before use, never provide more personal information than legally required, and consider using established cryptocurrency exchanges through verified mobile apps instead of unfamiliar ATMs.
4. Deepfake Video Extortion Schemes
The advancement of deepfake technology has enabled scammers to create highly convincing fake videos of tourists in compromising situations, leading to sophisticated extortion schemes that can devastate victims both financially and emotionally. These scams typically begin with seemingly innocent interactions: a friendly local offering to take photos, a charming stranger suggesting a video call, or even hidden cameras in compromised hotel rooms or vacation rentals. Using publicly available photos from social media profiles, scammers can create realistic deepfake videos showing tourists in explicit or embarrassing situations that never actually occurred. The extortion phase begins when victims receive these fabricated videos along with threats to share them with family, friends, employers, or social media networks unless substantial payments are made, usually in untraceable cryptocurrencies. The psychological impact is severe, as victims struggle to prove the videos are fake while fearing the social and professional consequences of their release. Some scammers enhance their credibility by demonstrating knowledge of the victim's personal life, travel itinerary, or professional relationships gathered through social media reconnaissance. The technology has become so sophisticated that even experts sometimes struggle to immediately identify deepfakes, making these scams particularly effective against unsuspecting tourists. To protect yourself, limit the personal information you share on social media, be cautious about allowing strangers to photograph or video you, use privacy settings to restrict access to your photos, and remember that legitimate authorities will never demand cryptocurrency payments for any reason.
5. Smart Luggage Hacking and Theft

The increasing popularity of smart luggage equipped with GPS tracking, USB charging ports, and Bluetooth connectivity has created new vulnerabilities that tech-savvy scammers exploit to track, access, and steal from unsuspecting travelers. These sophisticated theft operations begin with scammers using readily available hacking tools to identify and connect to unsecured smart luggage within airports, hotels, and tourist areas. Once connected, they can access the luggage's location data, disable security features, remotely unlock zippers or compartments, and even monitor the owner's travel patterns through connected smartphone apps. The most advanced schemes involve scammers who follow targeted luggage using GPS coordinates, waiting for optimal theft opportunities when bags are left unattended or during chaotic travel situations. Some criminals have developed specialized devices that can quickly override smart luggage security systems, allowing them to access contents within seconds while appearing to be legitimate travelers. The stolen data often extends beyond physical items, as many smart luggage systems store personal information, travel itineraries, and even payment details that can be used for identity theft or future targeting. Additionally, scammers may use compromised luggage systems to install malware on connected devices when owners charge their phones or tablets through infected USB ports. To protect yourself, always use strong, unique passwords for smart luggage apps, regularly update firmware, disable unnecessary connectivity features when not needed, never store sensitive information in luggage apps, and consider using traditional luggage with high-quality physical locks for valuable items.
6. Fake Emergency Alert Scams

Scammers have begun exploiting tourists' natural concern for safety by creating fake emergency alerts that appear to come from legitimate government agencies, hotels, or travel companies, designed to create panic and prompt immediate financial action. These sophisticated scams typically arrive via text message, email, or push notifications and claim urgent situations such as natural disasters, terrorist threats, political unrest, or health emergencies that require immediate evacuation or protective measures. The fake alerts often include official-looking logos, government seals, and urgent language designed to bypass rational thinking and prompt immediate action. Victims are typically directed to call specific phone numbers, visit fraudulent websites, or download malicious apps that promise safety updates or emergency assistance. Once contact is established, scammers pose as emergency officials, hotel security, or government representatives who demand immediate payment for emergency transportation, temporary accommodation, medical supplies, or expedited visa processing. The urgency created by these fake emergencies prevents victims from taking time to verify the information through official channels, making them particularly vulnerable to financial exploitation. Some variations include fake hotel evacuation notices that direct guests to leave their rooms immediately, allowing accomplices to burglarize abandoned accommodations, or false medical emergencies that require expensive immediate treatment. To protect yourself, always verify emergency information through multiple official sources, contact your embassy or consulate directly, never provide payment information during emergency situations without verification, and remember that legitimate emergency services never demand immediate payment via gift cards, wire transfers, or cryptocurrency.
7. Social Media Geo-Tag Exploitation

The widespread practice of sharing real-time travel experiences on social media platforms has created unprecedented opportunities for scammers to exploit geo-tagged posts, check-ins, and travel itineraries to target tourists both digitally and physically. These sophisticated operations involve scammers who systematically monitor popular travel hashtags, location tags, and social media posts to identify wealthy tourists, track their movements, and gather intelligence for various fraud schemes. By analyzing posted photos, scammers can determine hotel locations, restaurant preferences, shopping habits, and daily routines, allowing them to position themselves for optimal targeting opportunities. The collected information enables highly personalized scams, from fake travel companion requests that reference specific locations the victim has visited, to fraudulent local business recommendations that lead to overcharging schemes or worse. Some criminal organizations use automated tools to scrape social media data, creating detailed profiles of tourists that include financial indicators, travel companions, and vulnerability factors such as solo travel or unfamiliarity with local customs. The most dangerous aspect of this exploitation is how scammers use real-time location data to coordinate physical crimes, from pickpocketing and theft to more serious safety threats when tourists are identified as being alone in unfamiliar areas. Additionally, scammers may use geo-tagged posts to determine when homes are empty, facilitating burglaries in the victim's home country while they're traveling. To protect yourself, disable automatic geo-tagging on all social media platforms, avoid posting real-time location updates, share travel experiences after leaving each location, use privacy settings to limit who can see your posts, and consider creating a separate, private travel account for close friends and family only.
8. Fake Travel Insurance Claims Processing
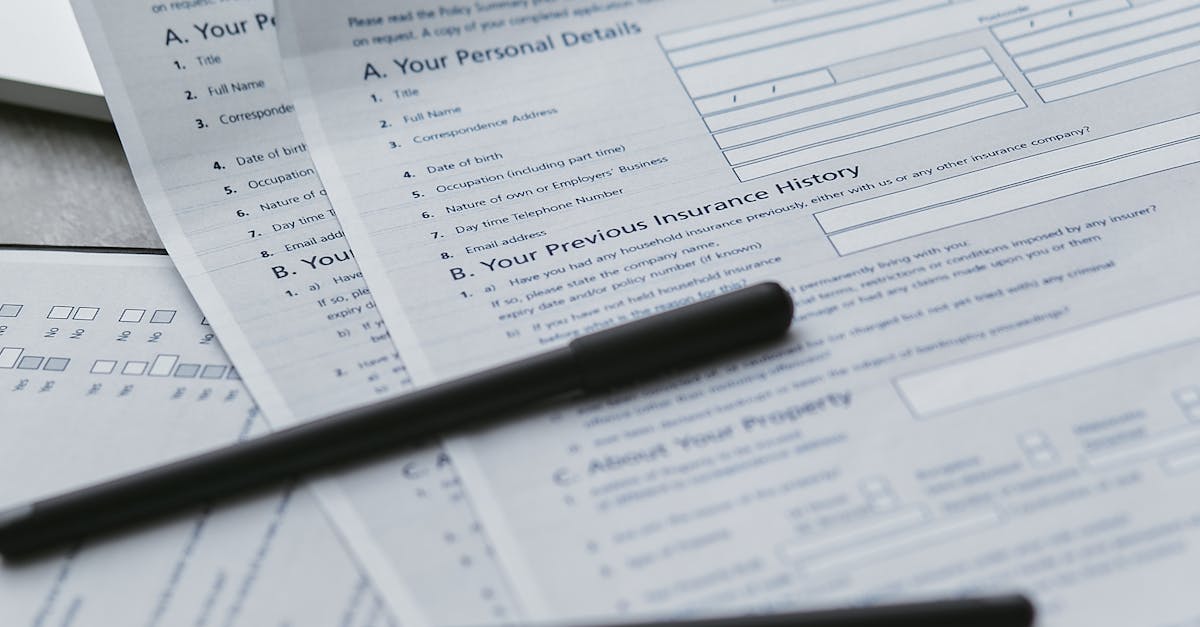
The complexity of international travel insurance has created opportunities for scammers to pose as legitimate claims processors, exploiting tourists who experience genuine emergencies or losses during their trips. These fraudulent operations typically contact victims who have filed legitimate insurance claims, presenting themselves as representatives from well-known insurance companies or third-party processing firms. The scammers demonstrate knowledge of the victim's actual claim details, often obtained through data breaches, social media monitoring, or partnerships with corrupt individuals within legitimate organizations. They offer to expedite claims processing, reduce documentation requirements, or provide immediate partial payments in exchange for processing fees, personal information, or banking details. The fake processors often create convincing websites, use official-sounding company names, and provide professional-looking documentation that mimics legitimate insurance communications. Victims are typically asked to pay upfront fees for claim processing, provide additional personal information beyond what was originally submitted, or transfer their claims to the fraudulent company for faster resolution. The scam becomes apparent only when victims realize their legitimate insurance claims have been compromised, their personal information has been stolen, or the promised expedited payments never materialize. Some variations involve scammers who proactively contact tourists who have posted about travel mishaps on social media, offering unsolicited assistance with insurance claims that seem too good to be true. To protect yourself, only communicate with insurance representatives through official channels provided by your insurance company, never pay upfront fees for claims processing, verify any unexpected contact by calling your insurance company directly using numbers from your policy documents, and be suspicious of unsolicited offers to expedite or improve your claims experience.
9. Augmented Reality Tourism Scams

The integration of augmented reality (AR) technology into tourism experiences has opened new avenues for scammers to exploit tourists through malicious AR applications and fraudulent virtual tour services. These sophisticated scams typically involve fake AR tourism apps that promise enhanced sightseeing experiences, historical information overlays, or interactive city guides but actually serve as vehicles for data theft, location tracking, and financial fraud. Scammers create convincing AR applications that mimic legitimate tourism tools, often using stolen branding from real tourism boards, museums, or travel companies to establish credibility. Once downloaded, these malicious apps request extensive permissions to access cameras, microphones, location data, and personal files, ostensibly to provide AR functionality but actually to harvest sensitive information. The apps may also prompt users to create accounts with personal details, payment information for "premium features," or social media integration that provides access to broader personal networks. Some AR scams involve physical components, such as fake QR codes placed near tourist attractions that direct visitors to download malicious AR apps or visit fraudulent websites. The most sophisticated versions actually provide limited AR functionality to maintain the illusion of legitimacy while secretly operating data theft or cryptocurrency mining operations in the background. Additionally, scammers may use AR technology to create fake virtual tours of popular destinations, charging tourists for experiences that either don't exist or provide minimal value compared to what was promised. To protect yourself, only download AR tourism apps from official app stores and verified developers, research app developers and read reviews before downloading, limit app permissions to only what's necessary for functionality, and be cautious of AR experiences that require extensive personal information or upfront payments.
10. Biometric Data Harvesting Schemes

The increasing use of biometric technology in travel, from airport security to hotel check-ins, has created new opportunities for scammers to harvest valuable biometric data from unsuspecting tourists through fake security checkpoints, fraudulent identity verification services, and compromised biometric devices. These sophisticated operations often target tourists at airports, border crossings, and high-security tourist attractions where biometric scanning appears normal and expected. Scammers set up fake security checkpoints or identity verification stations that closely mimic legitimate installations, complete with official-looking signage, uniformed personnel, and professional-grade scanning equipment. Tourists willingly provide fingerprints, facial scans, iris patterns, and other biometric data, believing they're complying with standard security procedures. The harvested biometric information is then sold on dark web markets, used to create fake identity documents, or employed in sophisticated identity theft schemes that can persist for years. Some scams involve compromised legitimate biometric devices where scammers have installed additional hardware or software to capture and transmit biometric data to criminal networks. The value of biometric data on illegal markets has skyrocketed because, unlike passwords or credit card numbers, biometric information cannot be easily changed once compromised, making it extremely valuable for long-term fraudulent activities. Additionally, scammers may use fake biometric enrollment services, claiming to help tourists pre-register for expedited security processing at various destinations while actually harvesting their biological identifiers for criminal purposes. To protect yourself, only provide biometric data at officially verified locations, verify the legitimacy of any unexpected biometric scanning requests, be cautious of "expedited processing" services that aren't officially endorsed by relevant authorities, and report any suspicious biometric collection activities to local security personnel or your embassy.
11. Fake Cultural Experience Overcharging

The growing demand for authentic cultural experiences has led to an explosion of fraudulent tour operators and cultural guides who exploit tourists' desire for genuine local interactions while charging exorbitant fees for substandard or entirely fabricated experiences. These scams typically involve individuals or organizations that present themselves as legitimate cultural ambassadors, traditional artisans, or indigenous community representatives, often using stolen credentials, fake certifications, or misrepresented affiliations with genuine cultural organizations. The fraudulent operators create elaborate backstories about their cultural heritage, community connections, and exclusive access to traditional ceremonies, artisan workshops, or sacred sites that aren't available to typical tourists. Victims are charged premium prices for experiences that may include visits to fake traditional villages populated by actors, participation in manufactured ceremonies with no cultural significance, or workshops with individuals who have no actual expertise in traditional crafts or practices. The scammers often employ high-pressure sales tactics, claiming limited availability or special cultural significance that requires immediate booking and full payment. Some operations involve elaborate staging, including fake traditional costumes, props, and settings designed to create Instagram-worthy moments while providing no genuine cultural value. The most insidious aspect of these scams is how they exploit tourists' genuine desire to respectfully engage with local cultures, turning this positive intention into a source of financial exploitation. Additionally, these fake cultural experiences can perpetuate harmful stereotypes and misrepresentations of actual cultural practices, contributing to cultural appropriation and misunderstanding. To protect yourself, research cultural experience providers through multiple sources, verify credentials and community affiliations independently, compare prices across multiple providers, read reviews from diverse sources, and consider booking through established cultural centers or tourism boards rather than individual operators approaching you directly.
12. Cryptocurrency Investment Travel Clubs

The intersection of cryptocurrency enthusiasm and luxury travel has created a new category of investment scams that target affluent tourists through exclusive "crypto travel clubs" and blockchain-based vacation investment schemes. These sophisticated operations present themselves as elite membership organizations that combine cryptocurrency investment opportunities with luxury travel experiences, often targeting tourists at high-end resorts, business conferences, and exclusive events. The scammers create impressive presentations about revolutionary travel platforms powered by blockchain technology, promising members the ability to earn cryptocurrency through travel activities, invest in vacation rental properties through tokenization, or participate in exclusive travel experiences funded by crypto investments. Members are typically required to make substantial initial investments in the club's proprietary cryptocurrency or tokens